The digital age has ushered in unparalleled advancements and convenience, but it has also opened the floodgates to a myriad of threats that target the very core of our digital existence: software. Software, the heart of every computer and digital system, is continually under siege by various malicious entities. Understanding these threats is not just about safeguarding our systems but also about ensuring the integrity, confidentiality, and availability of our digital information.
Cybersecurity in the Age of Sophistication
Among the plethora of software threats, one that stands out for its uniqueness and engagement is the Plane Game, a notable entrant in the online gaming scene. The check Plane Game, offers a dynamic and interactive gaming experience where players navigate a plane with the objective of earning money. This game exemplifies the innovative use of software to create immersive experiences. However, it also serves as a reminder that as software becomes more sophisticated and integrated into our daily lives, the need for robust security measures becomes paramount. The Plane Game, while offering entertainment and potential financial gains, also requires users to be vigilant and ensure that their interactions with the game are secure and protected from potential threats.
Malware: The Ever-Evolving Threat
Malware, or malicious software, is a broad term that encompasses various types of software designed to harm or exploit any programmable device, service, or network. Cybercriminals continuously develop new malware variants to bypass security measures. These can range from viruses and worms, which can replicate themselves and spread to other devices, to ransomware, which encrypts a user’s files and demands payment for their release. The sophistication of malware is such that it can hide its presence from users and security tools, making it one of the most significant threats in the software landscape.
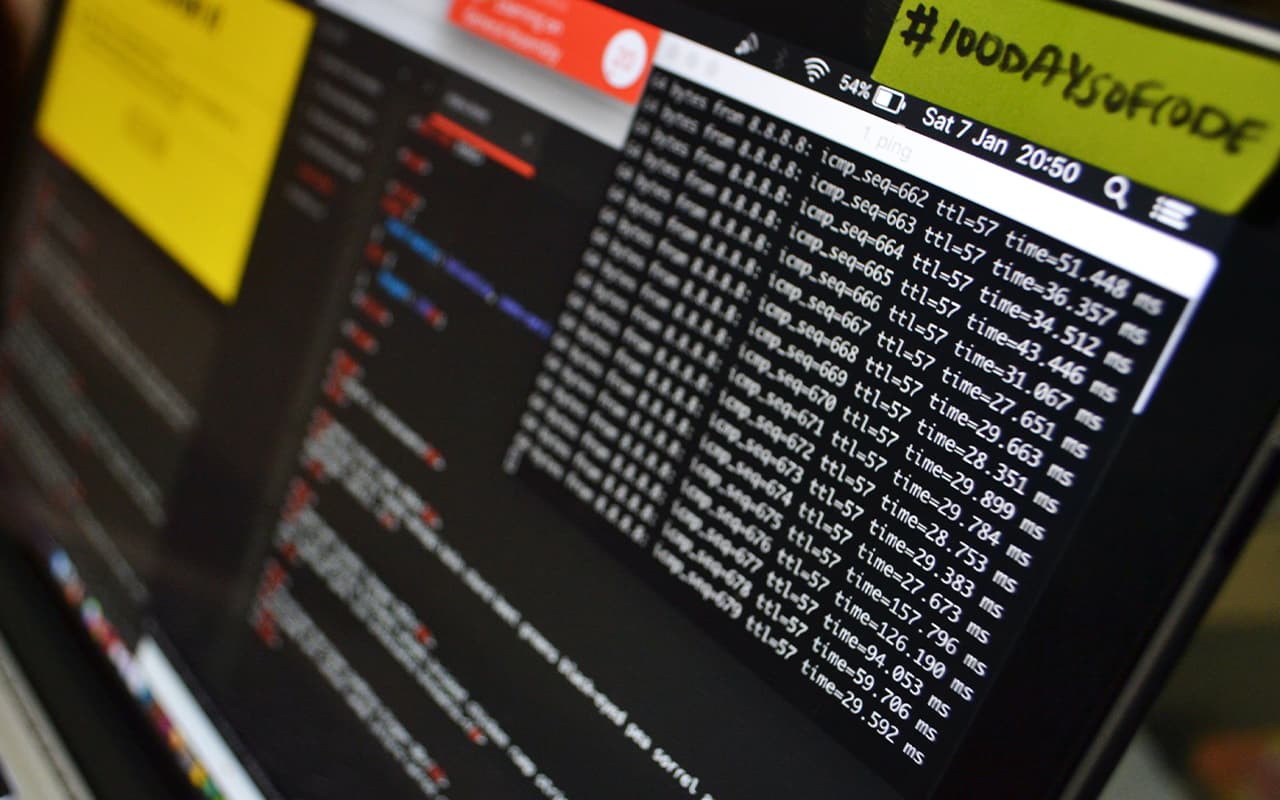
Detecting and Mitigating Malware
Protecting against malware involves a multi-faceted approach. Regular software updates and patches are crucial, as they often include fixes for security vulnerabilities that malware exploits. Comprehensive antivirus solutions can detect and remove malware, while user education on safe online practices can prevent malware from gaining a foothold in the first place.
Phishing Attacks: The Deceptive Danger
Phishing attacks stand as one of the most insidious forms of cyber threats facing individuals and organizations alike in the digital age. These attacks employ deceitful tactics to lure unsuspecting users into providing sensitive personal and financial information. By masquerading as legitimate entities—be it through emails, social media messages, or fake websites—phishers exploit the trust and sometimes the naivety of users. The deceptive nature of phishing makes it a particularly dangerous threat, as it relies more on manipulating human psychology than on technical vulnerabilities.
Strategies to Combat Phishing
Awareness and education are the primary defenses against phishing. Users should be skeptical of unsolicited communications asking for sensitive information and verify the legitimacy of requests through independent means. Employing spam filters and security software that identifies and blocks phishing attempts can also reduce the risk of successful attacks.
Software Vulnerabilities: The Hidden Flaws
Software vulnerabilities are flaws or weaknesses in a computer program that can be exploited to cause harm, such as unauthorized access or damage to the system. These vulnerabilities can exist due to errors in design, development, or configuration. Attackers exploit these weaknesses to carry out various malicious activities, making it imperative for software developers and users to identify and patch these vulnerabilities promptly.
Patch Management and Security Best Practices
Regularly updating and patching software is key to protecting against exploits targeting vulnerabilities. Software developers should follow secure coding practices and conduct thorough testing to minimize the introduction of vulnerabilities. Users should enable automatic updates when available and remain informed about known security flaws and patches for the software they use.
Conclusion: A Call to Vigilance and Action
The digital landscape is fraught with threats that target software from multiple angles. From the innovative yet vulnerable domains like online gaming exemplified by the Plane Game to the traditional but ever-evolving threats of malware, phishing, and software vulnerabilities, the need for comprehensive security measures has never been more critical. It is a collective responsibility that involves developers, users, and organizations working together to implement robust security practices, educate on the importance of cybersecurity, and remain vigilant against the constant evolution of digital threats.